-
-
Platform
-
Company
-
-
-
Commercial
- Industry Collaboration
- Solutions
- Industries
-
-
-
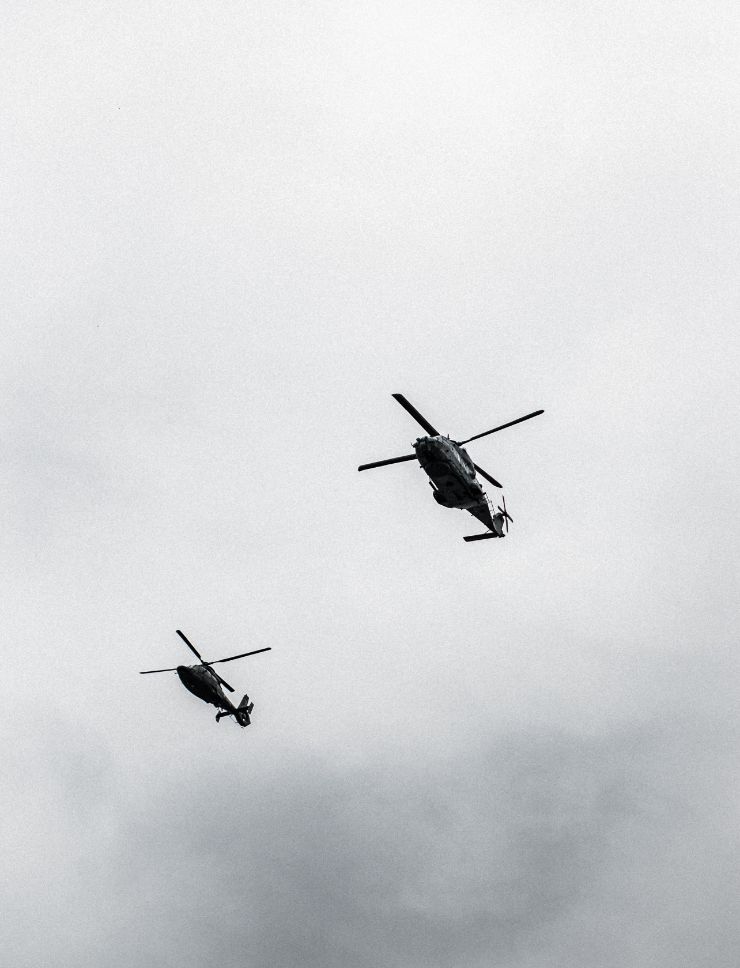
Government
-
© 2025 Fortress Information Security. All rights reserved